Today's Goal: USE-AFTER-FREE
(And the general PLOT of Mom's Spaghetti)
Let's FEEL how Use-After-Free might be something exploitable.
Sub-goal: The basic script setups we need

Don't like this style? Click here to change it! blue.css
Our compass through all of this is the desire for the following comfort food:
You're babies today and we're going to learn the warmth and love of the dining room table. So that as you venture into the wilderness you'll do your best to recreate this ritual in ever harsher environments.
I'll include this reminder in each of the heap class notes.
Let's FEEL how Use-After-Free might be something exploitable.

This is a typical CTF style setup. Where we have this sort of smallest possible CRUD (Create, Read, Update, Destroy) setup.
Here is a sort of starter pwntools script for this kind of problem:
One last thing... I'd like to run this against a slightly OLDER glibc, because they add more and more sophisticated protections over time.
Here is a version of everything linked to glibc 2.31: Baseline.zip
(This baseline, BTW, is level 1 of project 3.)
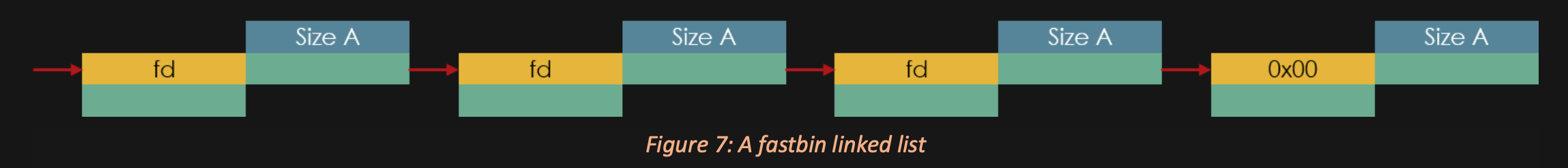
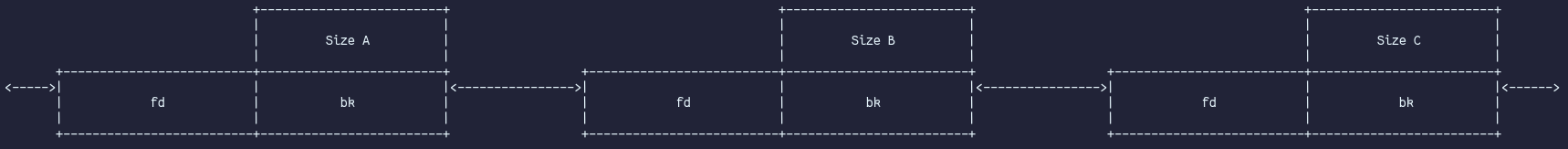
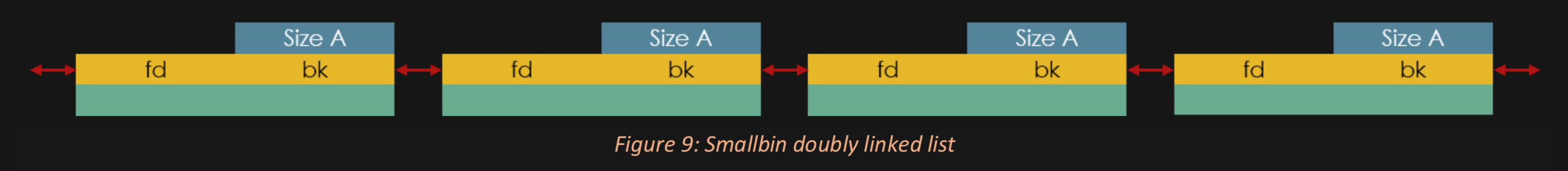
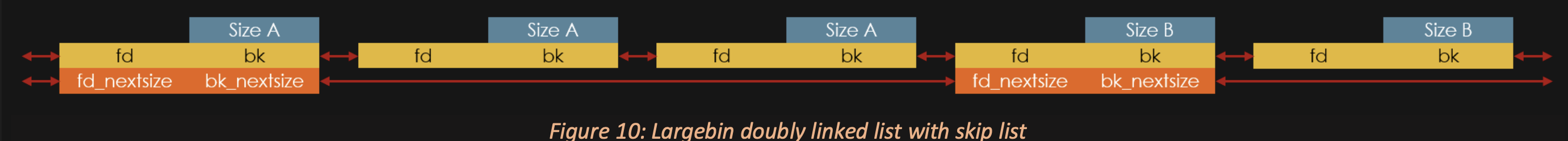
All we're going to do is mess around with linked lists.
Here are the samba notes we're going to try:
Our job is to corrupt a linked list in order to try to get a Write-What-Where.
I'll do this in more detail soon but I wanted to capture the vibes we're after before diving into all the details.
I'll link to these reference materials in each of the heap class notes.